DraftKings Continues Pursuit of DDoS Attackers
Among the more interesting business-side revelations in recent days was the news that last month’s wave of DDoS (Distributed Denial of Service) attacks targeting several online-poker and gambling sites was even more widespread than first realized, and included a company not traditionally among the targets for such attacks in years past. This new target was DraftKings, the US and global market leader in daily fantasy sports (DFS), which is now branching out into traditional single-event sports betting as well.
Without digging too deeply into the how and why for the moment of DraftKings and its primary niche rival, FanDuel, getting into traditional sports wagering when DFS suppposedly wasn’t “real” gambling, let’s look at last month’s DDoS attacks aimed at DK and the company’s energetic response to it, which is in the process of taking on an international flavor.
 As our readers likely recall, August was the Month of the DDoS-ing. It began with three days of bogus traffic aimed at the Winning Poker and America’s Cardroom, then moved over to PartyPoker and on to PokerStars. Then, it turned out that at least two other traditional online-gambling sites, PaddyPower and Winamax, had also experienced attacks, with Paddy acknowledging the “technical issues” on social media.
As our readers likely recall, August was the Month of the DDoS-ing. It began with three days of bogus traffic aimed at the Winning Poker and America’s Cardroom, then moved over to PartyPoker and on to PokerStars. Then, it turned out that at least two other traditional online-gambling sites, PaddyPower and Winamax, had also experienced attacks, with Paddy acknowledging the “technical issues” on social media.
And then there was DraftKings. Most often, attacked sites and networks have learned to endure, resigned to the truism that sooner or later, the online assaults usually cease. For DK, though, it may have been relatively new, and the attacks occurred just a couple of weeks before the site was set to begin accepting its first real-money action on regular-season NFL games. If you’re aware of the deep financial holes currently occupied by DraftKings, FanDuel, and virtually all other corporate DFS players, the 2018 NFL season getting underway represents a vital financial lifeline the site can’t afford to see threatened.
So DraftKings fought back, legally, by getting a court order against the Buffalo (NY) ISP, ColoCrossing, through which much of the DDoS attack traffic traveled. That DDoS attack began on August 7, according to a federal complaint soon filed by the company. That move was made necessary by ColoCrossing’ refusal to divulge the identity of the person or persons associated with the accounts and ISPs addresses logged by DraftKings as being part of the attacks. ColoCrossing wasn’t the only third-party service provider named in the complaint; also listed as potential parties of interest were ARIN (which distributes and manages IP addresses around the globe), Google, Verizon, T-Mobile, NetActuate, and ColoCrossing’s corporate parent, Minnesota-based Deluxe Corporation.
The thing is, it’s easy enough to log the IP addresses of computers used in the attacks, but it’s much more difficult to identify the culprits behind them. And sometimes the reporting is wrong as well. This feature, for instance, claims that the complaint DraftKings filed sought the identities of ten suspected attackers, but that’s not quite right: The complaint lists “John Doe” defendants 1-10, with the 10 being a reasonable upper bound as to how many people took part in the attack, since it’s usually done by one person or a small, interconnected group.
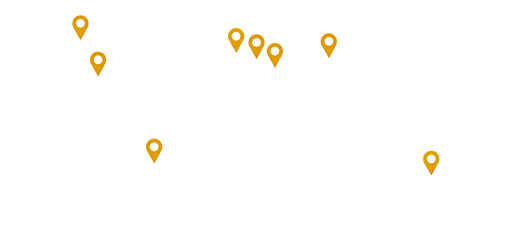
The DraftKings complaint, in fact, lists 37 separate IP addresses as being part of the attacks. It’s an interesting list:
Attacking IP Addresses Geographic Location
ip_static_ban-172.245.73.229 ElkGrove IL USA
ip_static_ban-23.94.108.162 ElkGrove IL USA
ip_static_ban-104.168.115.90 NJ USA
ip_static_ban-192.3.250.111 Dallas USA
ip_static_ban-198.12.106.118 ElkGrove IL USA
ip_static_ban-172.245.73.201 Buffalo USA
ip_static_ban-23.95.49.196 LA USA
ip_static_ban-104.168.95.214 LA USA
ip_static_ban-104.168.114.8 NJ USA
ip_static_ban-23.95.49.242 LA USA
ip_static_ban-192.3.76.116 Romania
ip_static_ban-23.94.20.118 Romania
ip_static_ban-104.168.92.158 LA USA
ip_static_ban-192.227.150.48 Ontario Canada
ip_static_ban-192.227.150.22 Ontario Canada
ip_static_ban-104.168.113.152 NJ USA
ip_static_ban-104.168.92.244 LA USA
ip_static_ban-192.3.253.16 Seattle USA
ip_static_ban-198.12.106.50 ElkGrove IL USA
ip_static_ban-104.168.95.186 LA USA
ip_static_ban-192.3.76.2 Romania
ip_static_ban-41.102.189.132 Algeria
ip_static_ban-46.148.147.160 Poland
ip_static_ban-37.8.4.27 Palestine
ip_static_ban-41.37.77.175 Egypt
ip_static_ban-176.224.83.81 Saudi Arabia
ip_static_ban-192.99.242.86 Venezuela
ip_static_ban-199.38.183.35 Reston VA
ip_static_ban-190.204.84.195 Venezuela
ip_static_ban-102.158.13.208 Tunisia
ip_static_ban-196.65.149.200 Morocco
ip_static_ban-174.205.21.40 Washington DC USA
ip_static_ban-107.178.196.211 Indiana USA
ip_static_ban-107.178.193.169 Indiana USA
ip_static_ban-107.178.193.189 Indiana USA
ip_static_ban-172.56.14.116 Houston USA
Traditional internet folklore tells us that most DDoS attacks are the results of thousands of virus-infected computers being trained on the targeted site at the same time. The above indicates that compromised computers are indeed central to the attack, but an attacker can cripple a site with dozens of computers, rather than thousands or tens of thousands.
The three Romanian IP addresses in the list are likely significant, because ColoCrossing soon complied with DraftKings’ demand for information and revealed that many of the other addresses to a Romanian proxy-service provider, HighProxies.com. DraftKings contacted the Romanian company and received no response, meaning that DraftKings will likely have to bring an action against that company in a Romanian court to learn more information about the attacker or attackers.
If this sounds like an exercise in peeling onions or playing whack-a-mole, well, it is. And yet it’s the only way to combat such attacks within legal systems. Even then, there’s no guarantee; years of attacks originating within Russia and attributed to the infamous Russian Business Network continued with tacit protection from organized-crime elements within Russia’s government, even if this attack against DraftKings looks more like a lone-wolf extortion project. Still, the last public chapter in this DDoS saga may yet to be written.



















COMMENTS